University of Nebraska restores access to several Canvas accounts following hack
LINCOLN, Neb. (KLKN) — The University of Nebraska on Friday restored access to several Canvas accounts following a nationwide hack of the platform.
According to the university, key integrated tools used for learning, teaching and assessment — including Yuja, Canvas Quizzes, Turnitin and Respondus — are now live and ready for use.
This all comes after the university said a threat actor had interrupted access to Canvas for users on all four NU campuses and campuses nationwide on Thursday.
SEE ALSO: University of Nebraska details nationwide hack to Canvas learning management system
Due to ongoing precautions, the following services have not been restored within Canvas:
- Microsoft 365
- Zoom
- Unizin Data Platform
- PeopleSoft “Import Grades from Canvas” feature
The university said functionality for Microsoft 365 and Zoom remains intact outside of Canvas and can be used on the respective platforms.
“Some users may notice a different appearance on the Canvas login page; please be assured that it is safe to use,” the university said.
According to the university, it will continue to assess security considerations and will restore additional Canvas services as soon as it is safe to do so.
“We appreciate your patience, flexibility, and understanding during this time as we work to fully restore services.”
On a FAQ page produced by Instructure, the parent company of Canvas, the organization said it identified unauthorized access on the platform on Thursday, which was tied to the same incident on April 29.
Instructure said the unauthorized actor made changes to the pages that appeared when some students and teachers were logged in through Canvas.
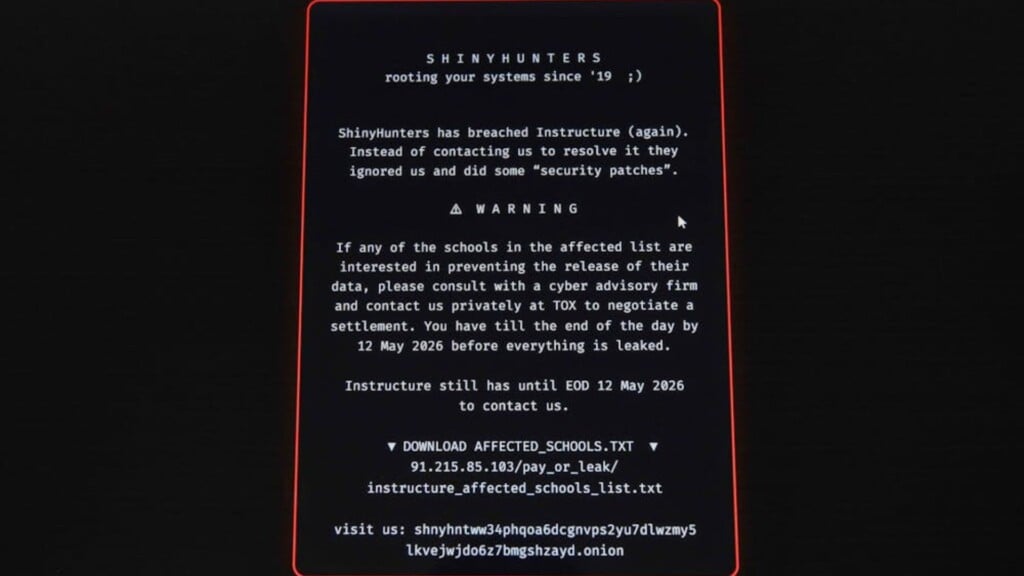
According to Penn State University’s student newspaper, The Daily Pennsylvanian, the cybercrime group ShinyHunters was locking users out of the interface.
Many students and staff have received the following message when logging onto the platform:
SHINYHUNTERS: Rooting your systems since ’19;)
ShinyHunters has breached Instructure (again). Instead of contacting us to resolve it they ignored us and did some “security patches”.
WARNING
If any of the schools in the affected list are interested in preventing the release of their data, please consult with a cyber advisory firm and contact us privately at TOX to negotiate a settlement. You have till the end of the day by 12 May 2026 before everything is leaked.
Instructure still has until EOD 12 May 2026 to contact us.
Out of caution, Instructure temporarily took Canvas offline into maintenance mode to contain the activity, investigate and apply additional safeguards.
Instructure has since confirmed that the unauthorized actor carried out this activity by exploiting an issue related to its Free-For-Teacher accounts. This is the same issue that led to the unauthorized access the prior week, according to the organization.
As a result, Instructure has temporarily shut down Free-For-Teacher accounts.
“These accounts have been a core part of our platform, and we’re committed to resolving the issues with these accounts,” the organization said. “In the meantime, Canvas is fully back online and available for use.”
Based on the investigation, Instructure said data taken in the April 29 incident includes certain personal information of users at affected organizations, including names, email addresses, student ID numbers and messages among Canvas users.
There is no evidence that passwords, dates of birth, government identifiers or financial information were involved.
Instructure said it has not found evidence that data was taken during Thursday’s incident, but the investigation is ongoing.
For more information on the data hack, visit Instructure’s website.